What is DKIM? All you need to know about DKIM
Domain Keys Identified Mail (DKIM) is a technological norm that helps deter spam, spoofing, and phishing from email senders and recipients. This is a type of email authentication that allows an individual to assert accountability for a message in a manner that the receiver may validate.
DKIM uses a “public-key cryptography” approach to verify that an email message has been sent from an authorized mail server to detect forgery and prevent harmful email delivery such as spam.
DKIM Signature- A DKIM signature is an email address header. The header includes values that enable a receiving mail server to confirm the email message by looking for the DKIM key of a sender and using it to check the signature encrypted.
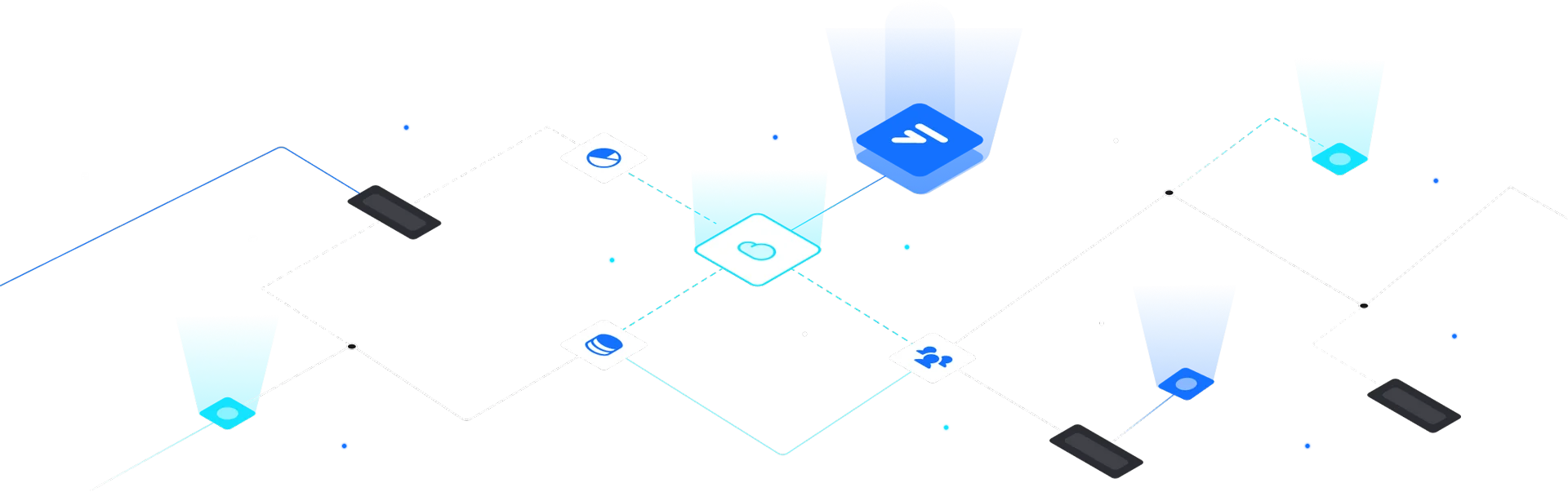
How it works ?
DKIM operates by applying a digital signature to an email message header. You can then check this signature against a shared cryptographic key stored in the DNS database of the company.
- A cryptographic key is released by the domain holders.
- This is formatted specifically as a TXT record in the overall DNS record of the domain.
- The application produces and applies the special DKIM signature to the document header after a letter is sent by an outbound mail server.
- Inbound mail servers then use the DKIM key to detect and decrypt the signature of the message and compare it to a fresh version.
- The message can be proven authentic and unchanged in transit if the values match, and therefore not forged or altered.
How is it related to SPF ?
DKIM and SPF are all protocols that require various aspects of email authentication. Complementary issues are addressed.
- SPF requires senders to specify which IP addresses for a particular domain are allowed to send mail.
- DKIM offers a digital signature and security key to ensure that an email message has not been faked or updated.
Advantages
- Bypass spam filters.
- Avoid getting phished.
- Improve Reputation.
Click here to read more about SPF.