2021 Roundup: 6 Worst Cybersecurity Attacks Witnessed Globally

2021 was indeed a year of transformation, shocks, and attacks. Every industry felt a different vibe and stress. Cybersecurity was something that was most talked about as people started working remotely and still continue to do so, with an increase in the threat landscape and a lot of open endpoints the stress on cybersecurity experts increased and the frequency and intensity of cyberattacks tool. 2021 has been a record-breaking year for the cybersecurity industry.
From security blemishes to software engineering failures, these high-profile IT fiascos unleashed true havoc this year and will no doubt continue to face next year, as well.
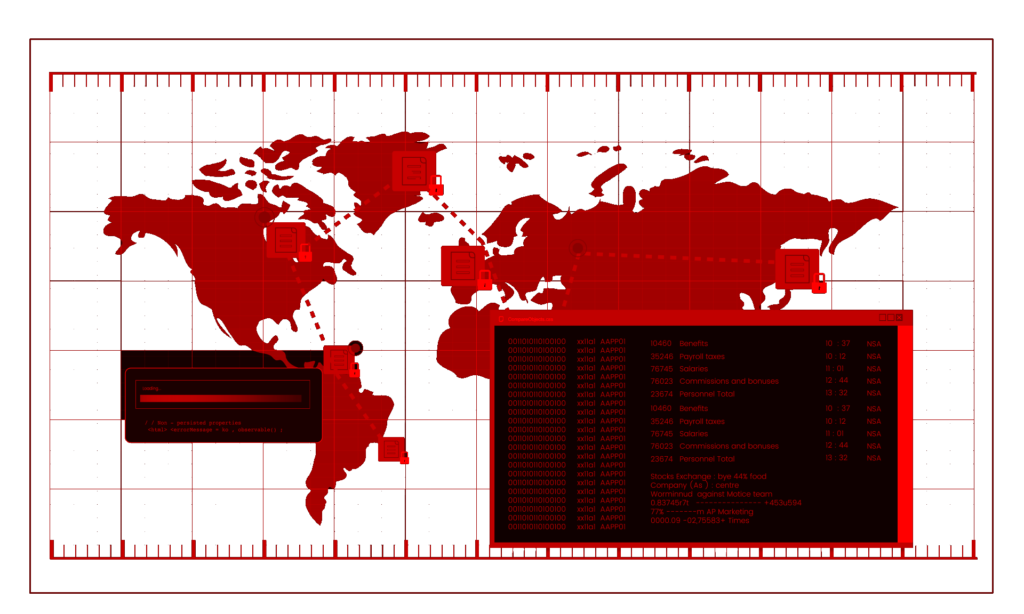
Here is a quick RECAP of major cybersecurity attacks in 2021
Before we move and predict how bad attacks can be in the coming, let’s look back at some of the worst cyberattacks of 2021. Though there were plenty of attacks and vulnerabilities that we could have included on this list, here’s our highly subjective review of 2021’s worst. These attacks are no less than a lesson for you.
1. Log4j Vulnerability sent ripples across the cybersecurity world in December
Log4J is different yet effective because it is not limited to one or two software, rather it is embedded in almost every Java-based product or web service and Java is the most used language the landscape is very wide making it difficult to protect and remediate easily. Because of its widespread use, the internet has been put on high alert as hackers increase their efforts to target weak systems.
The flaw (CVE-2021-44228) exists in versions Log4j 2.0-beta9 to Log4j 2.14.1 and can be exploited in multiple ways. The Apache Foundation initially released a new version of the tool (Apache Log4j 2.15.0) to address the issue but then had to release another update shortly thereafter because the first update did not fully protect against denial-of-service (DoS) attacks and data theft.
Click here to read more about the specifics and remediation for Log4J.
2. Colonial Pipeline became a victim of a Ransomware Attack
Colonial Pipeline got hit by a ransomware attack that resulted in shutting down pipelines on the East Coast, it was started when a hacker group identified as DarkSide accessed the Colonial Pipeline network The hack was more concerning as the pipelines were used to move oil from refineries to industrial markets making it more of a nation-security topic. US President Joe Biden had to declare a state of emergency.
The attackers stole around 100 gigabytes of data within a two-hour window. Following the data theft, the attackers also infected the Colonial Pipeline IT network with ransomware that affected many computer systems, including billing and accounting. Colonial Pipeline had to pay DarkSide hackers to get the decryption key, enabling the company’s IT staff to regain control of its systems
3. SolarWinds Orion Vulnerability
The SolarWinds attack became one of the largest nation-state supply chain attacks to date. The attack originated from SolarWinds’ Orion network management software and ended up becoming nation-state adversaries. The fallout of this hack almost affected thousands of global organizations, some were U.S. federal agencies like the Treasury Department and the Pentagon and a lot of the Fortune 500.
According to the official SolarWinds Security advisory, not everyone was vulnerable to the attack, those users using Orion software were vulnerable to the attack, especially the ones that updated their software in March. Nearly 18K customers have updated and were attacked.
4. Accenture Consulting Giant Breached by LockBit
Earlier this August Consulting giant Accenture was hit by a ransomware attack LockBit, though the attack was known since July news of the attack started to surface in August. LockBit 2.0 is the latest version of ransomware. LockBit was targeting many firms for a long time but this time the target was Accenture and the attack came with a price tag of $50 million. As one of the world’s largest consulting firms, $50 million is probably less concerning than the potential reputational damage, losing money was secondary for Accenture that too when the company itself works with cybersecurity and advises clients on their cybersecurity strategies and practices.
Here is an interesting infographic on LockBit 2.0.
5. Kaseya Attack, Supply chain attacks became a new normal
REvil is a Russian Ransomware gang that used two gaping flaws to break into software from Florida-based Kaseya to break into about 50 managed services providers (MSPs) that used its products, REvil hit more than 20 Texas municipalities through a shared provider two years ago, but only demanded $2.5 Mn in total ransom but to Kaseya, they asked $70 Mn to reverse the damage
Check out our interesting Carousel on REvil Ransomware.
6. Microsoft Exchange
Earlier this year in March, Microsoft detected multiple zero-day exploits that were being used to attack on-premises versions of the Microsoft Exchange Server. Within the next few days of this detection, 30,000 organizations in the US were attacked as hackers used several Exchange vulnerabilities to gain access to email accounts and elevate privileges on the Exchange PowerShell backend, allowing the attacker to perform unauthenticated, remote code execution, install web shell malware. Users were warned of these active exploitation attempts, though these vulnerabilities were patched earlier this May, including deploying LockFile ransomware on compromised systems.
One-size-fits-all solutions are no more effective; rather a holistic cybersecurity approach is what is needed. We advise you to frequently improve and evolve your methods and techniques of protecting your and your client’s most sensitive data.
Wishing you a happy and secure new year 2022 ahead!






