OWASP TOP 10 Explained: Broken Authentication

Broken Authentication is the second most important flaw in the ranking of OWASP Top 10. Using this loophole, an attacker may take control of the device user accounts. In the worst case, they may be helped to gain full mastery of the system.
The probability of broken authentication is not limited to a fixed attack pattern or a particular code flaw. User functions related to authentication and session management are frequently improperly enforced, allowing attackers to manipulate passwords, keys, or session tokens, or leverage other design vulnerabilities to presume the identity of other users on a temporary or permanent basis.
Broken Authentication Examples:
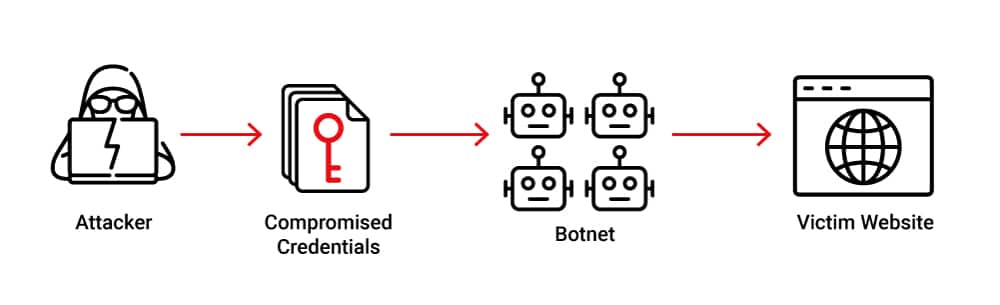
Credential Stuffing
The intruder has a common set of default passwords and usernames in Credential Stuffing. They will use this list to manipulate the passwords to sign in to legal passwords. It is advised that users change their default usernames and passwords to be safe against these attacks. An intruder can also create a list of Custom Passwords through different tools in Linux, such as CRUNCH, based on his previous target knowledge.
Unhashed Passwords
A shift of clear-text password to encrypted words from which an attacker may be fooled is called password hashing. What an attacker does so that an intruder will intercept a user request since all of them are on the same network. One can lose Account Permission & Secrecy using this strategy.
Misconfigured Session Timeouts
The case where the user logs out of the account and the intruder has the user’s key. You can still have access to that account using the session key. These glitches are referred to as Misconfigured Client Timeout.
How to prevent of Broken authentication attacks?
Enable Multi-Factor Authentication
Multi-Factor Authentication (MFA) is a security mechanism that needs more than one authentication process from different categories of token to validate the identity of the user for a login or other operation. MFA blends two or three professional credentials:
- What the user knows (His credentials)
- Anything that the user owns (Security tokens received from the SMS / authenticator app)
- What the user is (Biometric verification)
Where appropriate, multi-factor authentication can be used to avoid automatic password stuffing, brute force, and compromised sessions from reusing attacks.
Prevent Poor & Default Password
Our program does not require users to make poor passwords. When a user is setting a password, we need to follow the password rules and search for weak passwords. We will match password length, difficulty, and rotation policies by adopting the NIST 800-63 B guidance section 5.1.1 for memorized secrets or other new, evidence-based password policies.
Implementation of the Strong Credential Recovery Method
User authentication and password recovery are the main areas chosen by attackers to execute Account Enumeration Attacks. User Enumeration Attack is the method of checking a list of usernames against a legitimate program. If our code returns various messages or URLs in specific situations, such as when the username does not appear where the username appears but the password is incorrect, etc., it is vulnerable to Account Enumeration Attacks.
To defend our application against these types of attacks, we will ensure that user authentication, password recovery, and API routes are protected against Account Enumeration Attacks by using the same messages on all tests.
Limit / Delay Successive failure of login attempts
A common vulnerability to web developers is a password-proof attack, also known as Brute-Force Attack. It’s an attempt to find a password by repeatedly attempting any possible combination of letters, numbers, and symbols before they find the right combination that works.An attacker can still find a password with a brute-force attack, although it could take years to discover it. Depending on the length and difficulty of the password, there may be trillions of different variations. To speed it up a bit, a brute-force attack might start with dictionary words or slightly changed dictionary words, since most people use them rather than a random password. These kinds of threats place our user accounts at risk and congest our website with unwanted traffic.
Let’s see how we can avoid these kinds of attacks:
- Account Lockout- While these attacks are easy to detect, they are not as easy to avoid. The most simple way to avoid brute-force attacks is to automatically lock accounts after a certain number of incorrect login attempts have been made.
- CAPTCHA- CAPTCHA is a software that helps us to differentiate between humans and machines. They are especially successful in preventing most forms of computer violence, including brute-force attacks. They work by introducing certain exams that are easy for humans to pass but hard for computers to pass. They should also infer with some certainty that there is a person at the other end. We can also apply a CAPTCHA to a user on consecutive unsuccessful login attempts.
- Logging- Last but still important, we will also report all errors and warn administrators to prevent password stuffing, brute force, or other forms of attacks.






