Understanding Critical Threat Vectors 2023

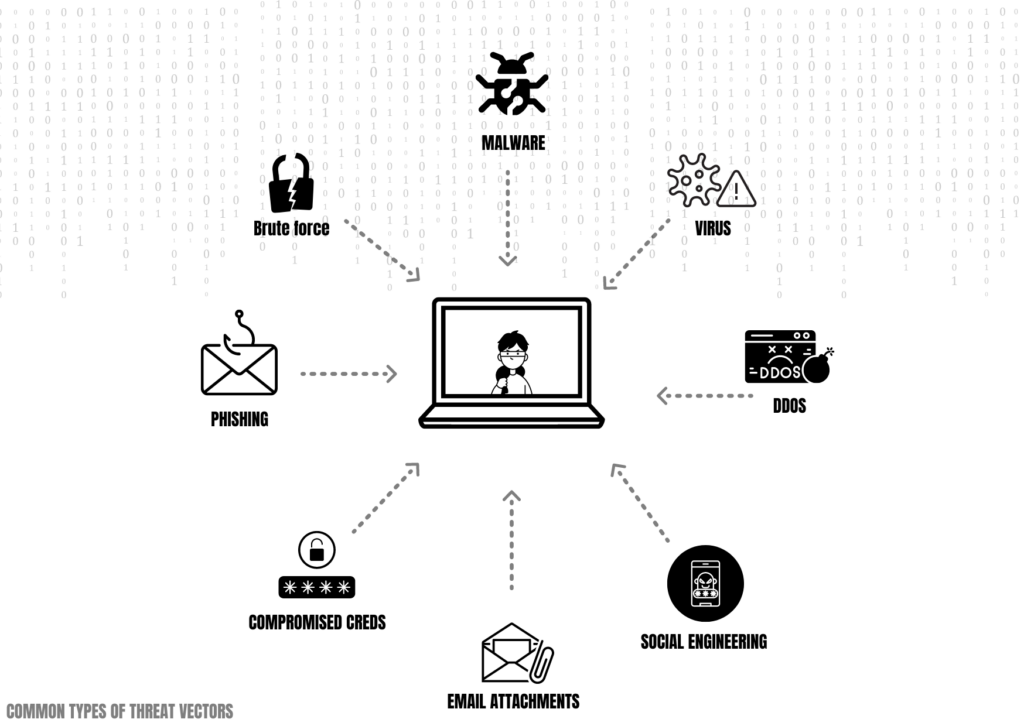
In the ever-evolving landscape of cybersecurity, one term that often arises is ‘threat vector.’ But what does it mean, and why should it be a central focus of your security strategy?
Simply put, a threat vector is a path or method used by cybercriminals to breach computer systems. These vectors might include malicious emails, infected websites, or even an employee’s actions within the organization.
Table of Contents
Types of Threat Vectors
Threat vectors can broadly be classified into external and internal vectors. External vectors refer to threats from outside the organization, such as hackers or malware. On the other hand, internal vectors originate within the organization, usually involving employees or internal systems.
External Threat Vectors
Phishing Emails
Phishing emails are fake emails which are sent by attackers to lure users into providing personal information or sensitive information such as passwords, usernames , Social security numbers etc. The attacker pretends to be someone you trust and sends a email requesting such information.
Weak and compromised Passwords
Weak passwords are often gateway for attackers to gain unauthorized access to internal systems or networks. This will provide attackers user privileges. Attackers will start from low level privileges and move up to higher privileges with admin level access.
Web Applications
Web applications are programs and services that organizations make available for access on the internet. These include email, office suites, search bars, photo editors, and comments modules. However, vulnerabilities are often found in web applications, including the application servers hosting apps and databases that store their data. Because web applications are accessible on the internet, attackers can freely exploit their vulnerabilities to steal data or gain unauthorized access. For example, using the popular SQL injection attack, in which malicious queries are made to an SQL database, attackers can extract data such as passwords (in encrypted form) and credit card details.
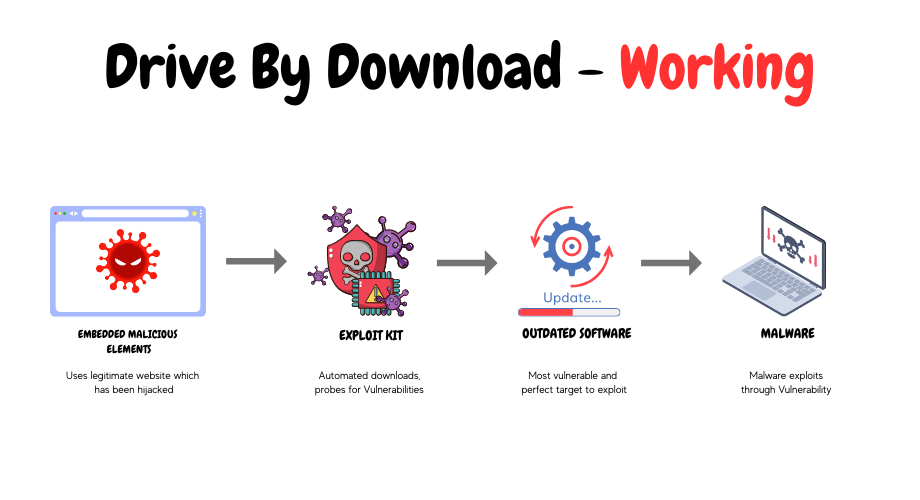
Drive by Download
A drive-by download occurs when malware is downloaded onto a device over the normal course of internet browsing, including legitimate and trusted websites. This happens because attackers have compromised the website with malicious code. In some cases, malware is downloaded after a user clicks on a link, a pop-up window, or advertisement. Attackers often masquerade their ads as attractive offers, warning messages, and browser update alerts to trick people into clicking. In other cases, malware is downloaded without any user interaction. This is made possible by vulnerabilities in the user’s internet browser that allows the attacker’s code to exploit it.
Remote Access Services
Remote access services allow users to connect to remote systems and networks. Commonly used remote access services include virtual private networks (VPN) and Windows remote desktop services, which provide remote workers with complete access to their workstation using another device. However, threat actors can scan for instances of these remote connections on the internet. Once these are discovered, they can hack the connection by breaking into the user’s account using a brute-force attack or exploiting misconfigurations and vulnerabilities in the service. A successful breach of a remote connection gives hackers access to workstations and network resources just like normal users
Social Engineering
One prevalent threat vector is social engineering. This tactic manipulates individuals into divulging sensitive information, often through phishing emails or spoofing attacks.
Malware and Viruses
Malware and viruses remain a significant threat. Cybercriminals often exploit software vulnerabilities or trick users into downloading malicious software.
Unsecured Wi-Fi Networks
Public Wi-Fi networks pose another risk, as cybercriminals can exploit these connections to intercept data or launch man-in-the-middle attacks.
Importance of Understanding Threat Vectors
Assessing Potential Vulnerabilities
- Understanding threat vectors helps organizations identify potential vulnerabilities in their systems. With this knowledge, they can fortify their defenses and prepare for possible attacks.
- As vulnerabilities can be a access point for an attacker to break through security, it is highly suggested fortify them using regular updates and security check.
Enhancing Protection Measures
- By understanding the various threat vectors, organizations can devise effective security strategies. This might involve implementing advanced cybersecurity technologies or fostering a security-conscious culture among employees.
Internal Threat Vectors: An Overlook
Employee Mishandling of Data
Employees can unintentionally become a threat vector. This may occur through simple mistakes, such as sending sensitive information via unsecured emails. Data loss or leaks can also be due to phishing attacks which are mainly focused on employees
Insider Threats
Insider threats are threats that come from within an organization in the form of negligent and malicious employees. Negligent insiders are those who are generally aware of the organization’s security policies but choose to ignore them. For example, revealing their passwords and connecting to the intranet using public wi-fi or personal VPNs. These actions inadvertently give attackers an easy route into organization’s systems and networks. Malicious insiders are those who carry out malicious activities on purpose. They may have been bribed by threat actors to steal data like trade secrets and customer information or help them load malware onto systems.
Threat Vector Identification and Management
- Identification of Threat Vectors:
- Discover potential threat vectors: Determine all possible entry points that attackers could use, such as network connections, email attachments, web applications, and physical access points.
- Assess vulnerabilities: Evaluate the weaknesses within each potential threat vector, including outdated software, misconfigurations, weak passwords, and unpatched systems
- Risk Assessment:
- Prioritize threats: Evaluate the potential impact and likelihood of exploitation for each identified threat vector. This enables the prioritization of mitigation efforts based on the level of risk.
- Quantify risks: Assign risk scores or ratings to each threat vector to understand their significance and potential impact on the organization’s assets, data, or operations.
- Management of Threat Vectors:
- Implement security controls: Deploy appropriate security measures to mitigate the identified vulnerabilities, such as firewalls, intrusion detection systems, access controls, and encryption.
- Maintain up-to-date systems: Ensure that all software, applications, and systems are regularly updated with the latest security patches and fixes to address known vulnerabilities.
- Enhance user awareness and training: Educate employees and users about common threat vectors like phishing attacks, social engineering, and malicious downloads. Promote safe online practices through security awareness training programs.
Transforming Threat Vector Understanding into Security Strategy
The Role of Real-time Detection
- Real-time detection plays a pivotal role in a security strategy. By identifying threats as they occur, organizations can respond quickly to mitigate damage.
- This could range from having security monitoring systems such as SIEM or End point monitoring systems which can keep monitoring the network activity for anything suspicious.
Importance of Comprehensive Asset and Network Visibility
- Complete visibility into network and assets is vital. It allows for quicker identification of vulnerabilities and provides insights into potential threat vectors.
The Human Factor in Threat Vector Management
Understanding Human Vulnerabilities
- Humans can often be the weakest link in a security strategy. By understanding human vulnerabilities, organizations can tailor their security measures to account for human error.
- As humans can be primary target for attacks such as phishing and other forms, they should be highly trained continuously for emerging security threats.
Training and Education
- A well-educated workforce is a strong defense against many threat vectors. Regular training on recognizing and responding to threats can reduce the risk of successful cyberattacks.
Threat Vectors and Cybersecurity Technologies
Utilizing Advanced Cybersecurity Tools
- Emerging technologies like artificial intelligence and machine learning offer new ways to combat threat vectors, identifying and responding to threats more efficiently.
Importance of Regular Software Updates
- Software updates often contain vital security patches. Regularly updating software can help protect against threat vectors that exploit software vulnerabilities.
The Future of Threat Vector Management
The Rise of AI and Machine Learning
- As cyber threats evolve, so too will the tools used to combat them. AI and machine learning will likely play a growing role in identifying and managing threat vectors.
Evolving Threat Landscape
- The threat landscape is ever-changing, with new threat vectors emerging as technology advances. Staying informed about these developments is crucial for maintaining an effective security strategy.
How Threat Vectors Impact Different Industries
Threat Vectors in Healthcare
Healthcare organizations, with their wealth of sensitive data, are often targets of cyberattacks. Understanding threat vectors can help these organizations protect patient information and maintain compliance with regulations like HIPAA.
Threat Vectors in Finance
Financial institutions face a unique set of threat vectors, from phishing attacks aiming to steal customer information to malware that targets banking systems. Understanding these threats is vital for safeguarding both customers’ money and the institutions’ reputation.
Threat Vectors in Transportation
Threat vectors in transportation encompass the pathways through which security breaches and attacks can occur. Common threat vectors include physical security risks like unauthorized access and sabotage, cybersecurity vulnerabilities in network infrastructure and connected vehicles, communication system issues such as radio frequency interference and GPS spoofing, supply chain concerns like cargo theft and counterfeit components, insider threats from employees, and the potential for terrorism targeting transportation infrastructure.
Case Study: A Successful Threat Vector Management Strategy
Scenario
Consider a healthcare organization that has experienced a series of data breaches. After conducting a threat vector analysis, they identified phishing emails as a significant threat vector.
Solutions Implemented
The organization implemented a two-pronged approach: first, they introduced an advanced email filtering system to detect and quarantine phishing emails. Secondly, they provided comprehensive training for staff to recognize and report phishing attempts.
As a result, the organization saw a significant reduction in successful cyberattacks, demonstrating the effectiveness of understanding and addressing threat vectors.
Key Takeaways: Threat Vector Understanding for Improved Security
Recap of Important Points
From recognizing social engineering attempts to understanding the risks of unsecured Wi-Fi networks, a comprehensive understanding of threat vectors enables organizations to develop more effective security strategies. It’s not just about technology – the human factor
plays a crucial role as well. Training and education are critical components of a well-rounded security approach.
Conclusion
In conclusion, understanding threat vectors is not just beneficial—it’s crucial for an organization’s security strategy. As technology advances and new threats emerge, this understanding will be even more essential. By keeping abreast of these developments and adapting accordingly, organizations can enhance their resilience against cyberattacks and protect their vital data assets.
What are three common threat vectors?
Three common threat vectors are
– Phishing Email
– Malwares
– Vulnerability exploitation
What is a threat vector?
A threat vector refers to the method or pathway through which an attacker can gain unauthorized access to a system, exploit vulnerabilities, or carry out a cyber attack. It is the means by which a threat is introduced into an environment or system, potentially leading to a security breach. Threat vectors can take various forms, including software vulnerabilities, social engineering tactics, malicious emails, compromised websites, or physical intrusion.






