Top 10 Attack Surface Management Tools: A Comprehensive Guide (2024)

Discover the top 10 Attack Surface Management tools that empower organizations to secure their digital infrastructure effectively. In this guide, we’ll explore these cutting-edge solutions designed to mitigate cyber threats and enhance overall cyber security posture. Learn how these tools can help you proactively manage and safeguard your critical assets from potential attacks.
Table of Contents
Introduction
Attack Surface Management (ASM) tools have emerged as essential assets in the defender’s arsenal, offering comprehensive solutions to identify, assess, and mitigate potential attack vectors. These tools play a critical role in helping businesses proactively manage their attack surfaces, safeguarding against cyber threats, and ensuring robust security postures. Here, we explore the top 10 Attack Surface Management tools, each distinguished by their features, capabilities, and effectiveness in defending against evolving cyber risks.
What is Attack Surface Management?

Attack Surface Management is a cyber security strategy with the goal of locating and reducing the weak spots, or “attack surfaces,” in a company’s digital infrastructure. It entails regularly assessing and monitoring the security threats connected to exposed assets, applications, and networks. Organizations can strengthen their defenses, lessen cyber threats, and improve overall cyber security resilience by proactively controlling these attack surfaces.
You can also read: Enterprise Security Best Practices: 10 steps to shield your organization from cyber threats
What is External Attack Surface Management (EASM)?
External Attack Surface Management (EASM) involves the ongoing process of identifying and evaluating internet-facing assets to detect vulnerabilities and irregularities. Utilizing EASM aids in comprehending the extent of exposure of these assets.
The realm of Attack Surface Management (ASM) is expanding, as evidenced by Gartner designating attack surface expansion as the foremost cybersecurity trend in 2022. Additionally, Detectify has gained recognition as a Sample Vendor in the External Attack Surface Management Category according to recent Gartner research.
Top 10 Best Attack Surface Management tools to consider
To that end, we present the top 10 Attack Surface Management tools that merit serious consideration. These tools empower businesses to proactively identify, assess, and mitigate vulnerabilities within their digital ecosystems, bolstering their overall security posture in an increasingly interconnected and threat-laden digital landscape.
1. Hunto AI
Hunto.ai stands out in the cyber security landscape for its robust approach to vulnerability management and compliance. The platform offers real-time monitoring automated compliance reports, assets inventory and alerts making it an ideal choice for organizations that must adhere to stringent regulatory standards. Its ability to swiftly identify vulnerabilities and ensure compliance positions it as a strong alternative for businesses focused on regulatory adherence.

Below we have highlighted a few points that are included in the services of Hunto.ai –
- Anti-Phishing & Anti-Rogue – Detects phishing/ rogue apps, fake domains, and fake social media accounts that can be requested for takedown, marked as false positive, or whitelisted.
- Data Leak & Sensitive Info Exposure – Leakage of proprietary and confidential data leading to monetary and competitive loss.
- Dark Web Threats – Detection of Sensitive data and PII information available for Sale on the dark web.
- Takedown Service – Remediation of threats through take-down assistance.
2. Tenable.io
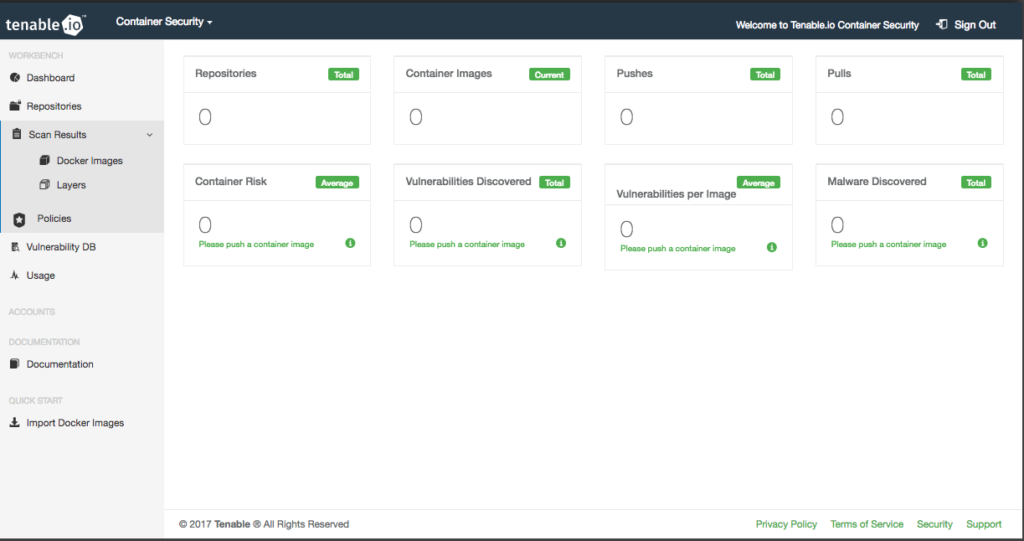
A well-known Attack Surface Management tools platform that has made a name for itself in the cyber security industry is Tenable.io. It offers a complete set of tools for locating, evaluating, and managing vulnerabilities throughout the attack surface of an organization. Tenable.io equips enterprises to proactively secure their digital infrastructure with real-time visibility into assets, continuous monitoring, and powerful vulnerability management tools.
Its cutting-edge analytics and reporting capabilities aid in prioritizing remedial operations, thereby lowering cyber threats. Tenable.io is a dependable option for businesses looking to strengthen their cyber security defenses and retain resilience against constantly changing threats thanks to its adaptability and scalability.
3. Mandiant

As among Attack Surface Management tools, Mandiant is well-known in the cyber security field. Mandiant offers comprehensive cybersecurity solutions and is renowned for its expertise in vulnerability management, threat protection, and policy compliance. It equips businesses with in-the-moment knowledge of their attack surfaces, enabling proactive risk mitigation.
Mandiant aids in strengthening security postures with its entire portfolio of services, which includes asset detection, vulnerability scanning, and compliance checks. It is a popular option for firms looking to manage and mitigate cyber risks successfully while remaining in line with industry laws due to its scalability and automation capabilities.
4. Microsoft Defender External Attack Surface
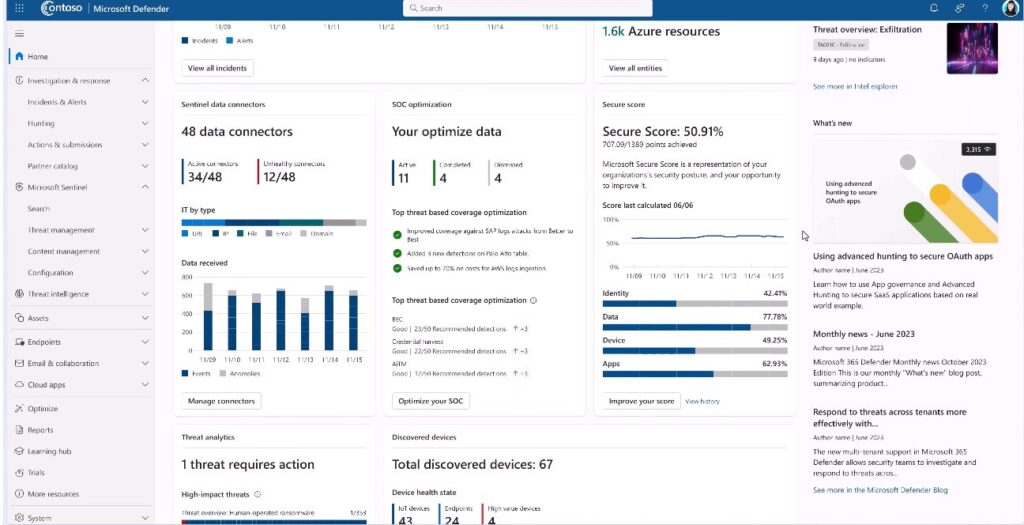
In the field of Attack Surface Management tools, which focuses on managing digital threats, Microsoft Defender is a well-known brand. This platform gives businesses the resources they need to quickly identify, address, and mitigate external risks. The areas of asset discovery, external threat monitoring, and incident investigation are where Microsoft Defender excels.
Businesses can obtain complete access to their digital assets thanks to this technology, which also quickly detects threats as they materialize and proactively identifies vulnerabilities. Microsoft Defender’s comprehensive service offering is essential in lowering an organization’s attack surface, boosting cyber security resilience, and protecting against the constantly changing world of hostile actors and digital threats.
5. Expanse
Expanse is a pioneer among Attack Surface Management tools, providing a worldwide internet inventory solution that enables businesses to keep up a high level of protection. Expanse excels at finding and keeping track of internet-connected objects, giving organizations important visibility into their attack surface. It assists in locating flaws, incorrect setups, and potential threats related to external digital assets.
Expanse contributes to lowering the attack surface and strengthening an organization’s cyber security defenses by continuously monitoring and evaluating the large digital landscape. Because of its ground-breaking methodology, businesses can actively manage and safeguard their most important assets in a dynamic and more linked digital environment.
6. Rapid7 InsightVM

One of the Attack Surface Management tools Rapid7 InsightVM provides a reliable vulnerability management solution. It provides real-time visibility into the resources and vulnerabilities of a business, assisting security teams in successfully prioritizing remediation operations.
To find and evaluate security flaws throughout the attack surface, InsightVM combines sophisticated scanning and assessment capabilities with threat intelligence. It speeds up the process of risk reduction and improves overall security posture with its automation and reporting solutions. In today’s dynamic and constantly changing threat landscape, Rapid7 InsightVM, a trusted option for businesses, is essential for proactively protecting digital assets and reducing cyber risks.
7. UpGuard
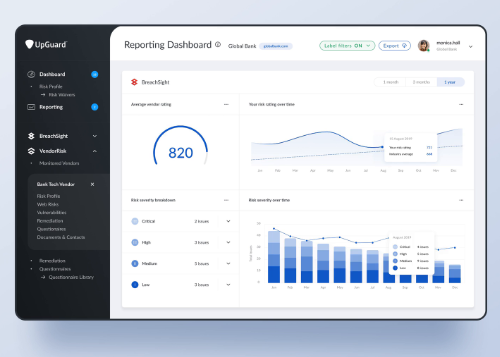
UpGuard is a pioneer in third-party risk evaluation and mitigation for Attack Surface Management tools. This platform gives businesses the ability to recognize and reduce risks related to third-party suppliers, partners, and interconnected digital assets. With regards to third-party risk management, UpGuard’s features include breach detection, cybersecurity ratings, and security questionnaires.
By evaluating and tracking the security postures of external entities, protecting against supply chain vulnerabilities, and preventing future data breaches, it offers insightful information regarding the attack surface of a company. Businesses may improve their overall security resilience with UpGuard in the increasingly connected digital world.
8. CyberGRX
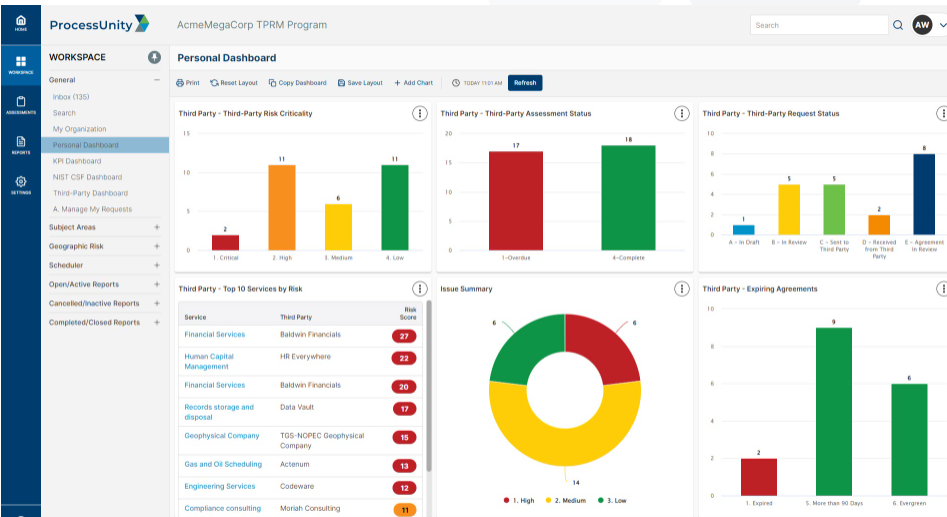
CyberGRX is a leader in third-party risk management and the field of Attack Surface Management tools. This platform provides an effective means of evaluating and lowering the risks connected to third-party providers, a vital part of contemporary corporate operations.
CyberGRX streamlines risk assessments and promotes cooperation between businesses and their vendors by offering a centralized and uniform assessment procedure. It gives companies the ability to proactively find supply chain weaknesses, improving overall cyber security resilience. CyberGRX provides businesses with the capabilities to protect sensitive data and strengthen their defense against potential cyber threats arising from their extensive digital environment through its data-driven insights and constant monitoring.
9. Kenna Security
A pioneer in cybersecurity, Kenna Security is renowned for its cutting-edge approach to Asset Attack Surface Management. By integrating vulnerability management and risk assessment, this platform gives enterprises a complete picture of their security status. Utilizing threat data and analytics, Kenna Security effectively prioritizes and fixes vulnerabilities while maximizing resource allocation.
Its data-driven insights help decision-makers make well-informed choices, thereby lowering cyber risks. Kenna Security is essential in strengthening an organization’s defenses by offering constant monitoring and useful recommendations. It serves businesses looking for a proactive, flexible solution to manage and reduce vulnerabilities across their ever-growing attack surface.
10. Axonius
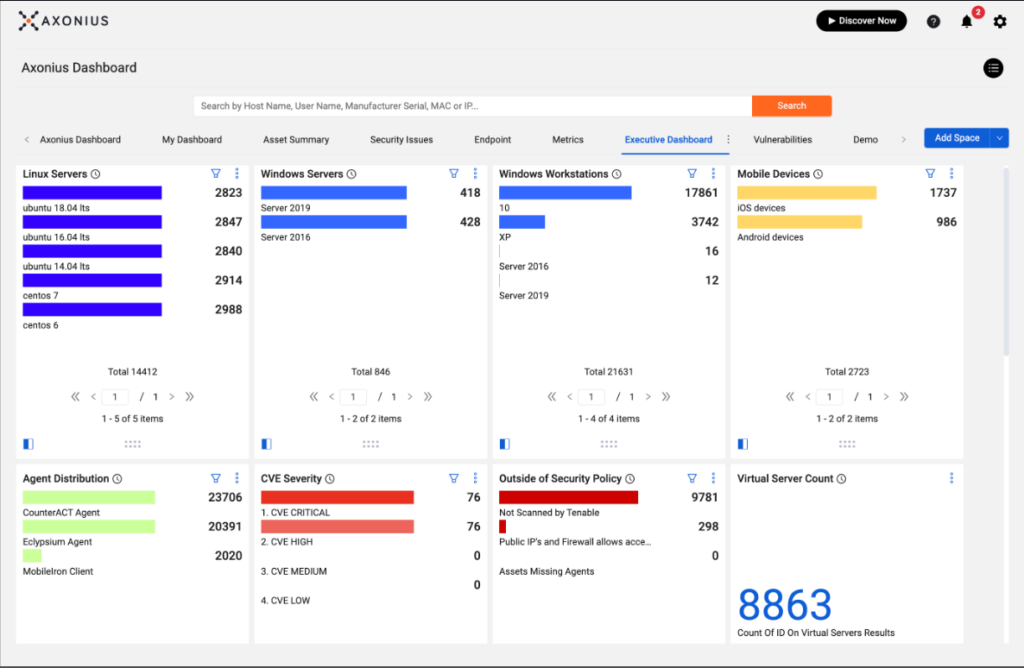
In the field of Attack Surface Management, Axonius is a major participant with a focus on asset management and security orchestration. Regardless of their location or nature, it provides real-time visibility into an organization’s assets, allowing enterprises to develop a thorough understanding of their attack surface.
Axonius assists in effectively identifying security holes and vulnerabilities by automating asset discovery and management. It streamlines security operations by integrating with already-in-use security technologies and workflows. By making sure that no asset is overlooked in a digital environment that is becoming more complicated and dynamic, Axonius enables enterprises to lower cyber risks, enforce security policies, and maintain a strong cyber security posture.

Important Features Of Attack Surface Management Software
Important Features of Attack Surface Management tools:
- Asset Discovery: Comprehensive scanning capabilities to identify all internet-facing assets, including websites, applications, APIs, and cloud services.
- Vulnerability Assessment: Robust vulnerability scanning and assessment to uncover potential weaknesses in discovered assets, including misconfigurations, outdated software, and known security vulnerabilities.
- Attack Surface Mapping: Visualization tools to map out the organization’s attack surface, providing a clear understanding of the scope and complexity of internet-facing assets.
- Continuous Monitoring: Real-time monitoring of changes to the attack surface, including new assets, configuration changes, and emerging vulnerabilities, to ensure proactive threat detection.
- Risk Prioritization: Prioritization of risks based on severity, potential impact, and exploitability, allows security teams to focus on addressing the most critical vulnerabilities first.
- Integration Capabilities: Seamless integration with existing security tools and platforms, enabling streamlined workflows and centralized management of security processes.
- Threat Intelligence Integration: Integration with threat intelligence feeds to enrich vulnerability data with context on emerging threats and known attacker tactics, techniques, and procedures (TTPs).
- Compliance and Regulatory Support: Built-in frameworks and templates to support compliance requirements such as PCI DSS, GDPR, and HIPAA, facilitating adherence to industry regulations and standards.
- Reporting and Analytics: Comprehensive reporting and analytics dashboards to track security posture, monitor key performance indicators (KPIs), and demonstrate compliance to stakeholders.
- Scalability and Flexibility: Scalable architecture and flexible deployment options to accommodate organizations of all sizes and infrastructures, including cloud-based, on-premises, and hybrid environments.
Conclusion
It is impossible to overestimate the significance of maintaining an organization’s attack surface in the constantly changing world of cybersecurity. The commitment to proactive security and risk reduction is exemplified by the top 10 Attack Surface Management products covered in this article. These technologies provide a range of capabilities to protect digital assets, from AttackIQ’s continuous security validation to Tenable.io’s complete vulnerability management. Visibility, threat detection, and asset management features are essential, and they are provided by Qualys, RiskIQ, Expanse, and others. Together, they enable businesses to strengthen their defenses, reduce vulnerabilities, and negotiate the treacherous terrain of cyberspace, ensuring resilience against the ever-changing threat environment.
You can also read: External Attack Surface Management
FAQs
What is an attack surface management (ASM) solution?
Attack surface management is the practice of identifying, assessing, and mitigating vulnerabilities and entry points in an organization’s digital infrastructure.
Which tool among attack surface management tools is best?
Rete.ai is a unified cyber security platform and one of the best attack surface management tools.
What is the surface area of a cyber attack?
The surface area of a cyber attack refers to the total range of potential entry points and vulnerabilities within an organization’s digital infrastructure that could be exploited by malicious actors.






