Table of Contents
Internal threats are rising. Is your security up to the task?
Before we move to Zero Trust Security principles, let’s take a step back and break a little stereotype of “Everything that is within our perimeter is secure and everything outside that perimeter is a threat”. Binary decisions are not great when we are dealing with a living, breathing system be it humans or security. Why trust then verify, when you can to do it another way around, i.e. verify then trust especially because it’s security.
Earlier many organizations worked inside a closed ecosystem, but now in the organization, every second data is being transferred between SaaS application, IaaS applications, IoT devices, and with COVID-19 N numbers of remote devices which has increased the premise beyond ends giving cybercriminals more entry points and they can cause a lot of damage while we are locating them.
So, we definitely need a new security paradigm shift.
“Let’s not trust anything by default because it is being operated from a place that you ASSUME safe.” The new security needs are now shifted to people and a small mistake by humans can cause huge damage.
Why is Zero Trust Strategy the need?
The workforce has never been this diverse the way it is today, it is so difficult to manage an open ecosystem. Organizations claim everything within the system is trusted but with the COVID-19, the question is where is the ecosystem and whom can I trust now. But now with Zero trust Security lessening the ecosystem is not possible but security shouldn’t be a hassle. Zero Trust Security not just verifies users continuously but also helps reduce data exposure in case of breaches.
Implementing a Zero Trust not only strengthens resiliency but also protects users, it is a proactive approach that detects threats and isolates them.
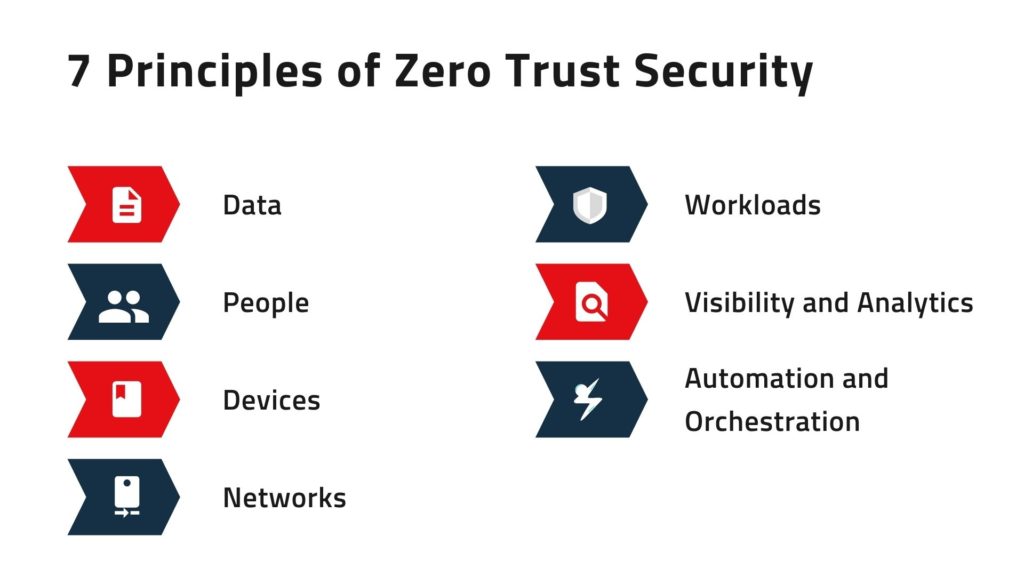
7 Focus areas to implement Zero Trust Model
- Data
- People
- Devices
- Networks
- Workloads
- Visibility and Analytics
- Automation and Orchestration
Zero Trust Networks
Attackers need to enter within your network to steal sensitive data. With Zero Trust networks it becomes extremely difficult, zero trust networks protect, segment, isolate and restrict the threats using the most revolutionary firewalls.
Zero Trust People
As we all know, humans can make mistakes, and hence they are the cause of most data breaches, mistakes can be anything from bad passwords, infrequent wrong clicks and can let anyone steal your credentials and impersonate you behind the screen. So, monitor your users’ activity within your network and protect them.
Zero Trust Devices
With everyone working remotely the number of devices within your network is increasing multifold and hence the need to secure the network is more important. Every connected device in your network is an entry point for the attackers and that can cause infiltration in your network. Your security team should be able to protect, isolate and have control over every connected device.
Zero Trust Data
Data is the ultimate target of the attackers and even the inside threats as with data anyone can do anything. Hence, it becomes more important for the security team to protect data before it becomes a breach. Your organization should have the option to know where the information resides, who can access it, what’s sensitive, and screen information to distinguish and react to possible dangers.
Zero Trust Workloads
The workload is running on a public cloud, which makes it even more difficult to detect and defend against dangers as it is a dynamic infrastructure and backend software that enables communication between the network and users.
Zero Trust Visibility and Analytics
This principle suggests the use of advanced technologies such as AI to automate the detection, protection, encryption processes which might anomaly detection and configuration control. Advanced threat detection, user behavior analytics and identify potential threats so that you can identify anomalous behavior.
Zero Trust Automation and Orchestration
With such a fast-paced life, no one is having time to wait for the threat to happen and then rectify it. With everything across being so dynamic it becomes even more difficult to detect threats and to make your network secure, you need to examine quickly and automate the whole zero trust system centrally.
So, when are you implementing the Zero Trust approach?
Since now you know being on the inside doesn’t mean being more trustable or vice versa rather it is highly ineffective. Your network is always hostile, so we need to control the access with the Zero Trust approach. To enhance the agility, incident response, policy accuracy, strategy precision of the organization, it becomes necessary for Zero Trust security architecture to incorporate with the organization’s security and IT environments.
We would like you to check our Cybersecurity Awareness Month special infographic:
https://www.tikaj.com/blog/what-is-qrishing-know-ways-to-prevent-it/
Learn more about Zero Trust :